Why 42,000 OpenClaw Deployments Are Running Without Security Hardening
The OpenClaw AI agent platform launched just four weeks ago. In that time, it has gathered 221,000 GitHub stars, built a community of 109,000 Discord members, and seen over 15,000 daily plugin installations through ClawHub. The adoption curve is unlike anything the AI industry has seen before.
But security has not kept pace with that growth. A Censys scan reveals more than 42,000 OpenClaw instances currently exposed to the internet without proper hardening. Security firms including CrowdStrike, Palo Alto Networks, Cisco, and Kaspersky have all issued advisories warning about the platform's attack surface.
The ClawHub marketplace sits at the center of the problem. Researchers at Koi Security and Bitdefender have flagged over 800 malicious plugins in the registry — roughly one in five of all available plugins. These are not theoretical risks. The ClawHavoc malware campaign, first detected in January 2026, has used weaponized ClawHub plugins to steal credentials, cryptocurrency wallets, and session tokens from compromised deployments.
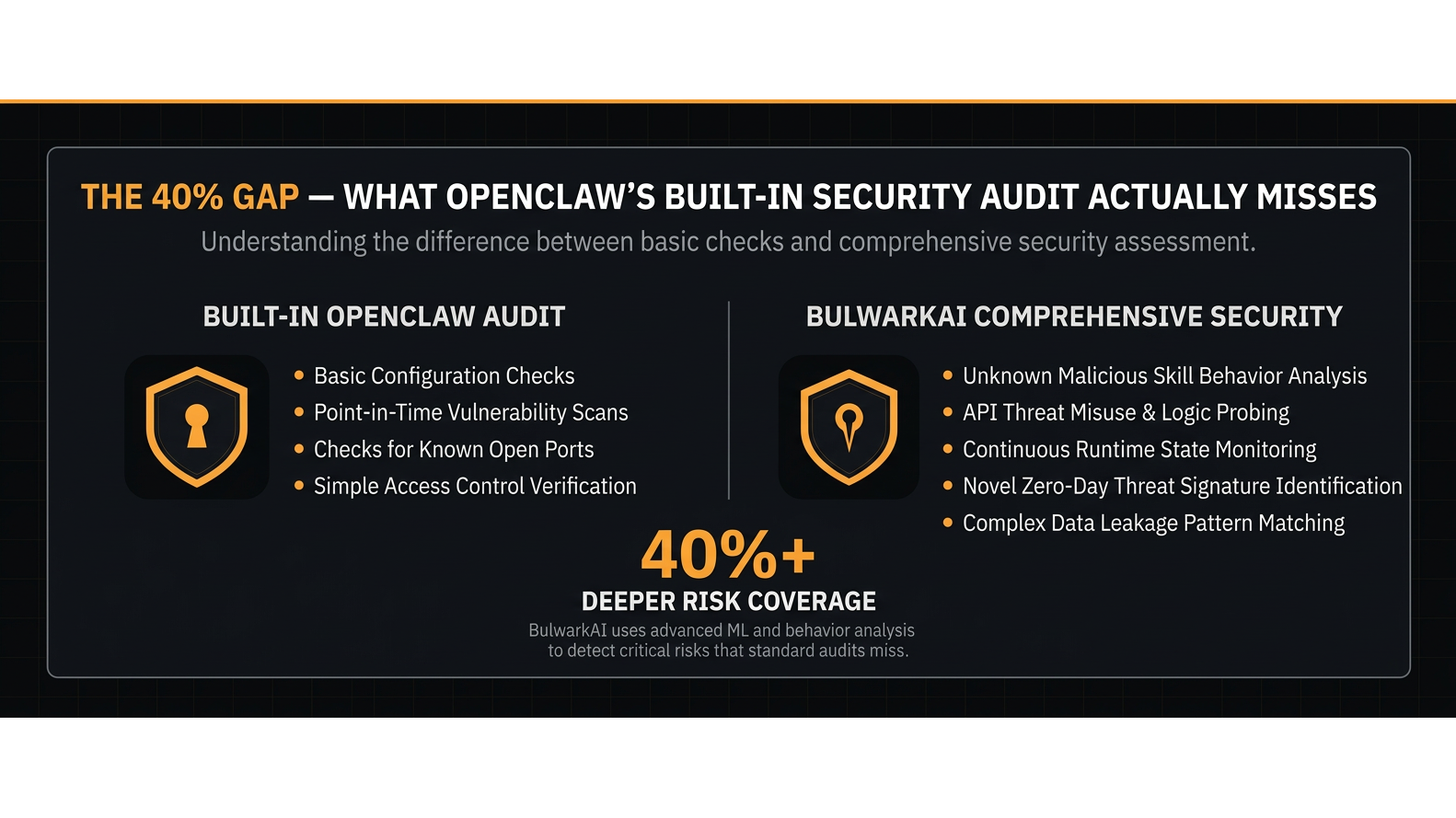
OpenClaw includes a built-in security audit command. Running it produces a report covering gateway configurations, permission settings, and known CVEs. For many users, this is the only security measure applied after deployment. According to analysis by BulwarkAI, a cybersecurity consultancy founded by platform security architect Peter Kwidzinski, the built-in audit catches approximately 60 percent of known threats.
The remaining 40 percent represents a significant blind spot. The built-in audit does not scan across multiple skill directories on the same system. It does not hash identity files to detect tampering. It cannot audit MCP server configurations for data exfiltration patterns. It misses persistence mechanisms like unauthorized LaunchAgents. And it has no capability to detect zero-width character injection in SOUL.md files, an attack vector documented by Zenity Labs.
Free tools from vendors like SentinelOne, Adversa AI, and Snyk improve coverage in some areas, but they share a common limitation: none of them personalize findings to a specific deployment. A security scan that flags 15 high-severity findings without context about which findings actually matter for a given setup leaves the operator guessing about priorities.
Peter built BulwarkAI to bridge this gap. The company offers three tiers of service. The Security Blueprint is a comprehensive hardening package containing deployment-specific configurations, detection scripts, an IOC database covering 824 malicious skills, and printable security checklists. The Security Audit adds personalized expert review, delivering a detailed report that references specific agents, skills, and integrations by name, along with a 30-minute video walkthrough. The Full-Service Hardening tier provides hands-on remediation where BulwarkAI accesses the deployment directly, applies all fixes, and tests everything before handing it back.
Organizations deploying OpenClaw for business operations face a choice between accepting the coverage gap in existing automated tools or investing in expert review. With the threat landscape evolving weekly and new malicious plugins appearing daily on ClawHub, the cost of delayed action continues to grow.
A free security scan is available at https://www.bulwarkai.io for anyone running an OpenClaw deployment who wants to understand their current exposure level.
BulwarkAI
City: Folsom
Address: Folsom, California
Website: https://www.bulwarkai.io
Comments
Post a Comment